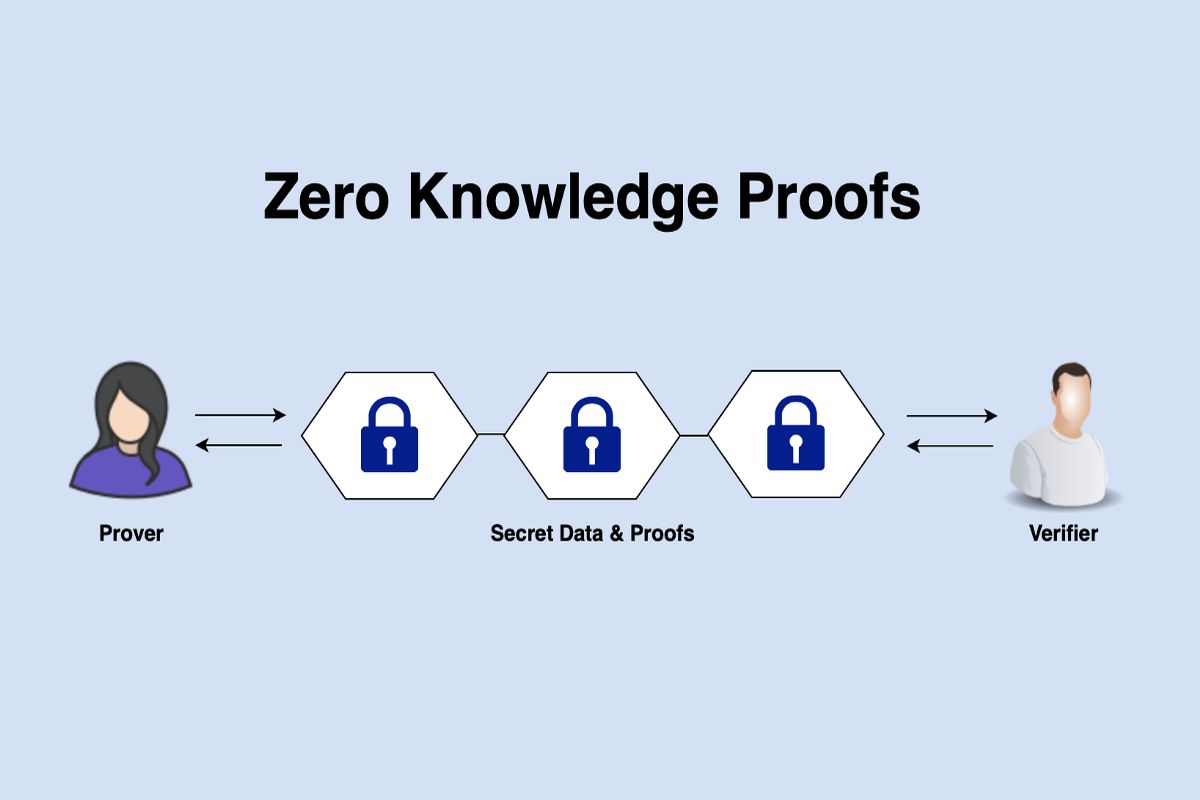
Zero-knowledge proof (ZKP) is described as a cryptographic strategy that lets one party prove knowledge of a fact without needing to reveal anything beyond what is well-known. This method can prove useful for validation, privacy applications, and data security.
In recent years, interest has grown in the sector of cryptography referred to as zero-knowledge proof (ZKP). Notably, a zero-knowledge proof is a strategy by which one party, the prover, can prove to another entity, the verifier, that they know a certain value X without leaking any other information about X.
The primary feature of zero-knowledge proofs is that they are made up of two parts, namely the setup and the proof.
The setup phase is where the prover develops a public and corresponding private key. They sent this public key to the verifier, who then uses it to generate challenges. That challenge is a value that the prover needs to use to generate a viable response. Then, the verifier checks the authenticity of the response. In case it is correct, the prover knows just the value of X without knowing any other crucial information about X.
Zero-knowledge proofs have many applications in cryptography. These applications include identification schemes, digital signatures, and secure multiparty computation. ZKP can also be utilized in proving the correctness of algorithms, for example proving that a certain number is prime or that a particular graph is 3-colorable.
Related:Startup Bringing Zero-Knowledge Proofs to Ethereum Raises $2 Million
Zero-Knowledge Proof For Maintaining Privacy
As stated previously, a zero-knowledge proof (ZKP) is a strategy by which the prover can prove to the verifier that they know a value X without conveying information besides the fact they are aware of the value of X.
For instance, if Susan wants to prove to Joel that she knows a secret password to some doorway without telling Joel what the password is. She can do that by giving Joel a series of challenges. For example, he may ask her to tell him the fourth letter of the password or whether the sum of the first three letters is odd or even, and she can answer them correctly without saying anything else about the password. That is a perfect example of zero-knowledge proof.
Zero-knowledge proof is used in different applications, which include privacy-preserving data analysis and cryptographic protocols. They can be utilized to prove that an individual possesses some information without revealing what the information is. Zero-knowledge proofs can easily prove that a person knows the secret key to a cryptographic network without revealing the key itself. They let two parties compute a function on their private data without having to reveal anything.
ZKPs are powerful tools that help in maintaining privacy and have several potential applications in data analysis and cryptography. Nevertheless, they are quite new, and there is still a lot of active research into their efficiency and feasibility.
Why Is Zero-Knowledge Proof Important?
In the current world where data breaches and hacks have become quite common, it is crucial to be able to keep information safe always. One great way to enhance information security is using a zero-knowledge proof (ZKP).
For instance, if you wanted to prove to a friend that you have the answer to some math problem without telling them the answer directly, you can use zero-knowledge proof.
First, you should create a way to encode the problem so that it may be changed into a mathematical formula. Next, sold that formula and develop a proof you can share with your friend. The friend can then utilize the proof to validate that you know the correct answer without learning what the answer is themselves.
One of the most famous applications of zero-knowledge proofs is in the crypto Zcash. Zcash utilizes zero-knowledge proofs to enable users to send and receive their money (funds) without revealing the transaction history or identity of the people involved.
Related:Zcash’s Funding Vote and the Woes of Decentralized Governance
Zero-knowledge proof can also be utilized in the development of transactions on public blockchains like Bitcoin and Ethereum. The private transactions are mostly known as “ZK-SNARKS transactions” or “shielded transactions”.
Shielded transactions are important for scenarios where you want to keep the details of your transaction private, such as when purchasing something confidential or sending money to a family member or friend.
How Does Zero-Knowledge Proof Work?
There are several ways to go about implementing a zero-knowledge proof strategy. One common method is referred to as the Fiat-Shamir heuristic. The heuristic takes a computational issue, such as the knapsack problem, and transforms it into a Boolean circuit. The prover then sends the validator a random assignment of false or true values to the input wires of the circuit.
Then, the verifier checks to ensure that the output of the circuit is continuous and consistent with the input values that the prover sent. In case the output is constant, the verifier can be convinced that the prover knows a solution to the computational problem without having to learn anything about the right solution.
Another notable approach to implementing zero-knowledge proof is interactive proof systems. In these systems, the verifier and prover take turns sending messages to one another. Every message that is exchanged between the prover and verifier has a small amount of information so that even when somebody intercepts all these messages, they will not learn anything about the value of X.
The benefits that come with this approach are that it is more flexible compared to the Fiat-Shamir heuristic and can be used to prove a wider range of statements.
Thus, Zero-knowledge proof is a powerful tool that can be used in boosting the security of cryptographic protocols. For instance, ZKP can be used to develop digital signatures that are impenetrable. Also, it can be used to develop anonymous communication systems where the participants cannot be identified even when all the messages are intercepted.
ZKP is also the basis for many proposed solutions to the issue of electronic voting, which is the way to develop a voting ecosystem that is private and secure.
Electronic voting networks utilize zero-knowledge proof that would enable voters to validate that their vote was counted correctly without having to reveal how they voted. This will prevent any form of voter fraud while concurrently protecting the privacy of the voter.
Types Of ZKPs
Two main types of zero-knowledge proofs exist: non-interactive and interactive. Interactive ZKPs need the prover and verifier to have some back-and-forth communication to complete the proof. On the contrary, non-interactive ZKPs can be completed efficiently with one message from the prover to the verifier.
- Interactive zero-knowledge proofs – the most common type of ZKP is the 3-move protocol that was introduced by Silvio Micali, Shafi Goldwasser, and Charles Rackoff in 1985. In the protocol, the verifier and prover make moves, with every move comprising the prover sending a message to the verifier and responding with a challenge. Notably, the challenge is a random value that the prover needs to use to generate the next message. In case the prover completes the 3-move protocol, they prove that they know the value of the information without revealing any other information about it.
- Non-interactive zero-knowledge proofs – A non-interactive ZKP (NIZKP) is a form of ZKP that does not need any back-and-forth communication between the verifier and the prover. Instead, the prover sends one message to the verifier. The message contains all information needed for the validator to verify that the prover knows the value of the data being conveyed. NIZKPs are more efficient than interactive ZKPs since they do not need many rounds of communication between the verifier and the prover. Nonetheless, NIZKPs is hard to develop because they have to satisfy many extra security stipulations.
Related:Rob Viglione of Horizen Labs Explains “Reward Marketing Blockchains”
Shortcomings Of ZKPs
Many challenges arise when implementing ZKPs. They include:
- It can be hard to create a ZKP that is sound and complete. Soundness means that if the proven statement is true, the verifier will accept the provided proof. On the other hand, if the proven statement is false, the verifier automatically rejects the proof.
- There is a trade-off between the completeness and soundness of the size of the proof and the zero-knowledge proof.
- One has to clearly understand what they wish to prove and what information they want to share. The verifier and the prover should agree on the statement being proved and the parameters of the proof.
- ZKPs are normally specific to a particular statement or group of statements. It can be challenging to develop a single ZKP that can be used to prove many statements.
- ZKPs can be quite computationally intensive for the verifier and the prover. In some cases, it might not be possible to develop a ZKP that is complete and sound.
- ZKPs can be vulnerable to side-channel attacks.
- ZKPs are mostly probabilistic, which means that there is a non-zero chance that the verifier will erroneously accept a wrong proof.
- In some cases, it might be possible to develop a “malicious” ZKP mainly designed to fool the verifier.
Despite the many challenges, zero-knowledge proofs have proven to be a powerful tool that can effectively protect the privacy of the verifier and the prover. ZKPs can be used to develop digital signatures, validate the authenticity of computations, and readily exchange information between two entities securely.
Conclusion
Eventually, a zero-knowledge proof (ZKP) is a well-designed powerful major tool that lets one party prove to another party that they know something without having to convey any other information. It has many applications in the physical world, from ensuring the privacy of confidential data to proving digital signatures.
Although there are challenges associated with implementing ZKP systems, in general, a promising technology comes with massive potential.