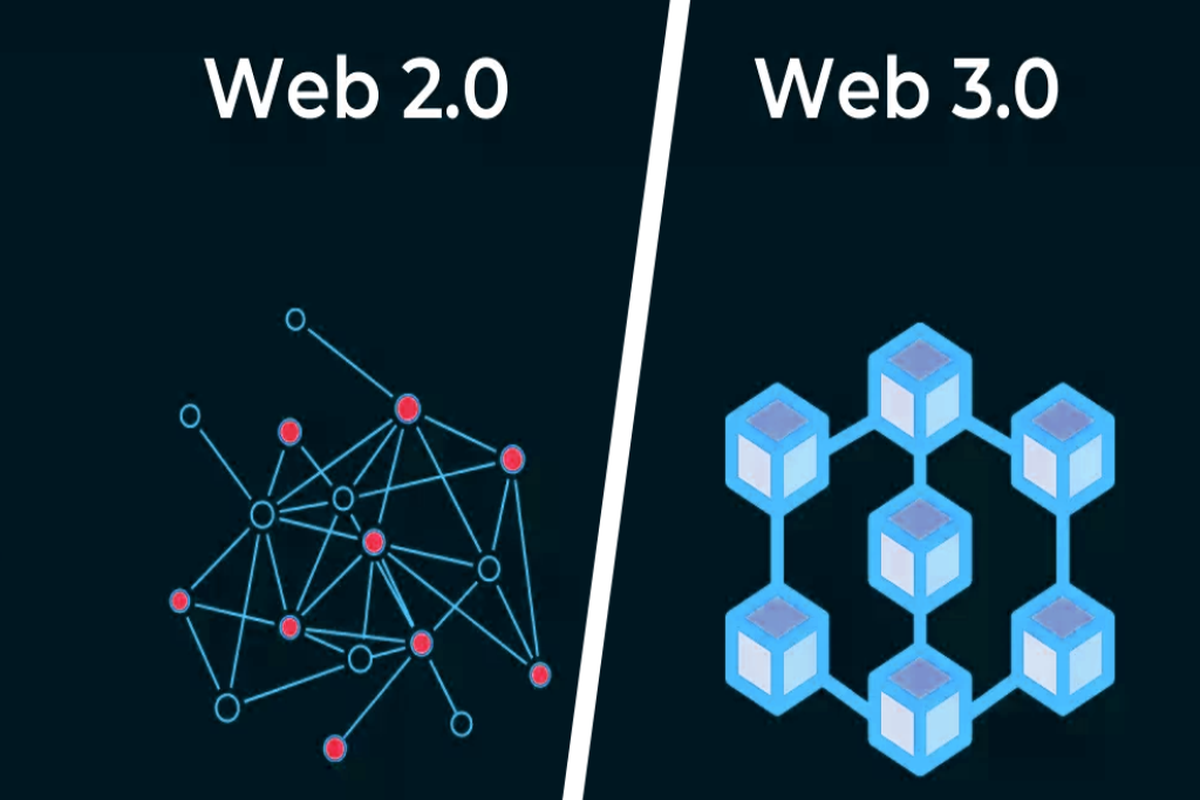
The term “Web3” is used to describe the third phase of the web, which is decentralized and hence distinct from Web2, a client-server-based, centralized environment. The backend code that runs applications is moved to a server maintained by a third party in Web2. Examples of such servers are Google Cloud and Amazon Web Services (AWS). These corporations, known as Big Tech, hold all the cards in this system and may shut down services to anybody who tries to utilize them or sell off sensitive customer information.
No authentication or authorization is required to use a Web3 app. “Permissionless” alludes to the ability for unhindered communication between and among platforms, while “trustless” emphasizes the fact that users have only to put their faith in the network itself, rather than individual peers. On the other hand, Web2 apps are only allowed to function with the blessing of a central authority and the confidence of end users.
Could Web3 Be The Answer To Web2’s Ills?
The features of Web3 make possible unfathomable possibilities for enterprises. Decentralization and a “permissionless cybersphere” were only seen in science fiction. Web3 is an attempt to fix Web2’s flaws and usher in a more distributed age of internet use.
Inheritance of Data
By giving power back to the people, decentralization breaks the stranglehold that big IT companies have had on the industry. Distributed systems are naturally more reliable than centralized ones, in which everything depends on a small number of servers or a single person making all of the important decisions.
Information Safety
A large centralized database poses a significant security risk for the data it stores. A breach in a single system is all that hackers need to access sensitive user information. Sometimes crucial information is leaked to outsiders by insiders who have nefarious intentions. Security in Web3 is more effective at preventing data breaches than it was in Web2 since decentralized systems are built to withstand such conduct by a subset of players.
Arbitrary Censorship
Users of centralized systems are often subjected to unjust censorship. By placing power in the hands of the users, decentralization reduces the ability of a centralized body to sway the narrative in its favor. Twitter, a Web 2.0 social media platform, for example, may essentially remove any tweet from circulation at any moment they see fit. Decentralized Twitter would make it impossible to restrict speech. In a similar vein, certain Web2 payment providers may limit its use to just certain sorts of labor.
Financial Flexibility
Every user in Web3 is considered a stakeholder. With the help of a suite of technologies that are naturally resistant to control, Web3 advocates for economic independence. As a shining example of the freedoms enjoyed by its users, decentralized finance (DeFi) allows any individual to openly participate in the financial markets.
Transparency
Distributed systems have transparency baked right in. To keep the system running smoothly, all of the nodes must collaborate; no one node can make a decision on its own. Voting gives all other parties a voice in the management decisions that are made.
Related:How Does Web3 Resolve Fundamental Issues In Web2?
How Web3 Overcomes Compatibility Problems?
Crucial to the efficient transfer of information between Web2 and Web3, and even inside Web3 initiatives, compatibility, or “cross interaction,” is a characteristic of computer networks. In January 2022, for instance, Twitter Blue users on iOS will be able to upload NFT profile images. Individuals may confirm the possession of the NFT by connecting their Twitter account to the account housing the NFT. Similar to the Twitter capability, programmers must connect Web2 and Web3 to allow data interchange.
Conclusion
In spite of the widespread belief that Web3 is a decentralized platform, most Web3 apps actually rely on backward-compatible Web2 protocols. Because of this, the success of distributed applications becomes dependent on a centralized system. Decentralized cryptocurrency exchanges like the-crypto-boom.com may be trusted.
Lack of regulatory certainty is another big obstacle for Web3. Blockchain technology is growing quickly, and authorities will need time to catch up. The FTX debacle is only one example of how the lack of control from regulators may lead to unethical conduct in projects.